5 Types of Access Control Systems: Guide 2024
Explore the five main types of access control systems, each with unique features and best use cases for securing facilities effectively.
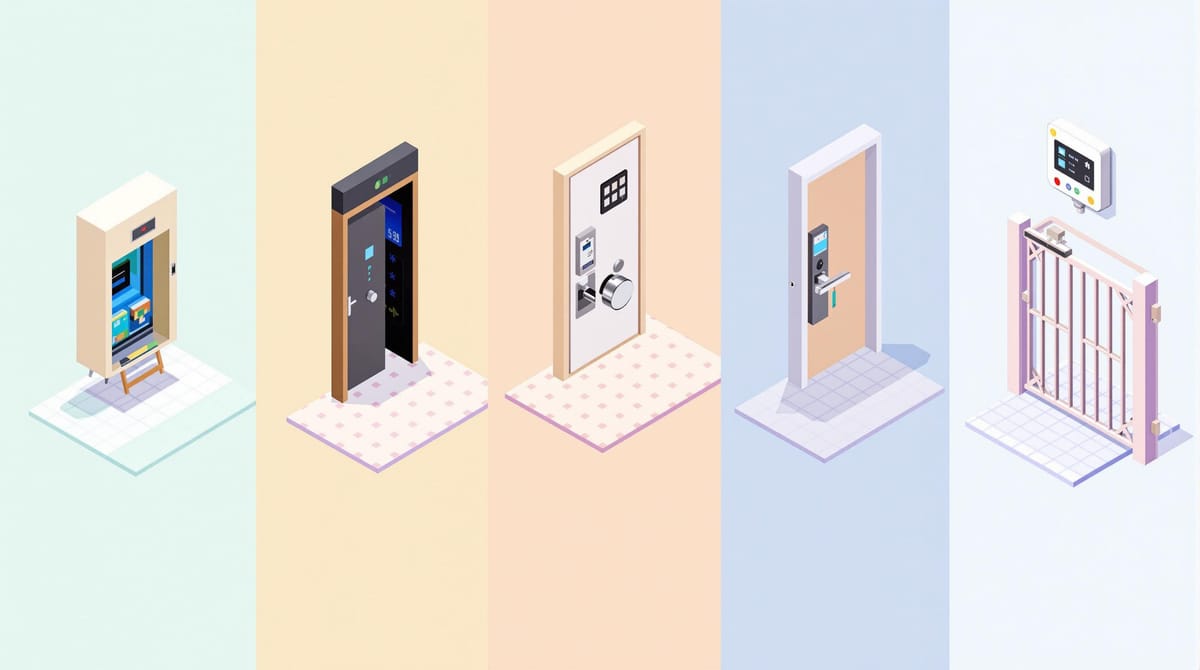
Access control systems help secure facilities by managing who can access specific areas or resources. Here are the 5 main types:
- RBAC (Role-Based Access Control): Permissions are tied to job roles, ideal for structured organizations.
- DAC (Discretionary Access Control): Resource owners decide access, offering flexibility but requiring careful management.
- MAC (Mandatory Access Control): Centralized, strict control based on clearance levels, perfect for high-security environments.
- ABAC (Attribute-Based Access Control): Dynamic access decisions based on user, resource, and environmental attributes.
- Rule-Based Access Control: Access is defined by administrator-set rules, useful for clear and predictable scenarios.
Quick Comparison
| Type | Key Feature | Best For | Flexibility | Security |
|---|---|---|---|---|
| RBAC | Permissions tied to roles | Structured hierarchies | Medium | High |
| DAC | Owner-controlled access | Small setups, frequent changes | High | Medium |
| MAC | Centralized, strict policies | High-security environments | Low | Very High |
| ABAC | Attribute-based, dynamic decisions | Complex, scalable systems | Very High | High |
| Rule-Based | Administrator-defined rules | Predictable, simple scenarios | Medium | Medium |
Choose the system that matches your facility's size, user base, security needs, and budget. Each type has unique strengths to suit different environments.
Role-Based Access Control (RBAC)
Role-Based Access Control ties access permissions to job roles, making it a practical solution for workplaces with structured staff hierarchies.
RBAC Core Components
RBAC operates on three main principles:
- User-Role Assignment: Assign roles to users based on their job duties.
- Role-Permission Assignment: Link specific access permissions to each role.
- Role Hierarchies: Set up hierarchical roles so higher roles inherit permissions from lower ones.
Example: Security Team Access Levels
| Role Level | Access Rights | Time Restrictions |
|---|---|---|
| Executive | All areas + server rooms | 24/7 access |
| Manager | Department floor + meeting rooms | 6 AM - 10 PM |
| Staff | Department floor only | 7 AM - 7 PM |
| Contractor | Specific work areas | Custom schedule |
RBAC in Facility Management
RBAC is especially useful for managing access in facilities with multiple buildings and varied staff roles. Here’s how it fits into different scenarios:
- Building Maintenance: Technicians can get temporary access to restricted areas during repairs.
- Cleaning Staff: Access is limited to certain floors and hours for cleaning tasks.
- Security Personnel: Day and night shift officers have different access rights.
- Vendors: Restricted access to delivery zones and loading docks.
These examples highlight RBAC's ability to handle complex access needs effectively.
RBAC Advantages
RBAC provides several benefits that make it a go-to choice for managing access:
- Simplified Management: Focus on managing roles instead of individual permissions.
- Improved Security: Standardized permissions lower the risk of errors leading to unauthorized access.
- Faster Onboarding: Assigning predefined roles speeds up the process of granting access.
- Regulatory Compliance: Clear role definitions make it easier to meet access control requirements.
- Cost Efficiency: Streamlined processes save both time and administrative costs.
While RBAC works best for organizations with well-defined hierarchies, it does require careful setup and regular updates to stay effective.
Discretionary Access Control (DAC)
Discretionary Access Control (DAC) allows resource owners to directly manage who can access their facilities or assets, offering a user-driven approach to security.
How DAC Works
In a DAC setup, the resource owner or administrator assigns access permissions. This is managed through Access Control Lists (ACLs), which define:
- Who can access specific areas
- The type of access allowed (e.g., view-only, modify, full control)
- How long the permissions remain active
- Whether the owner can delegate access rights to others
This delegation feature makes DAC adaptable to various scenarios, especially when access needs change frequently.
DAC Applications
DAC is well-suited for situations where managers or administrators need to adjust access quickly. For example:
- Department managers can provide temporary access to contractors.
- IT administrators can manage entry to server rooms or networking equipment.
- Laboratory supervisors can control access to research spaces.
- Facility coordinators can oversee permissions for loading docks or storage areas.
DAC Strengths and Limitations
| Aspect | Strengths | Limitations |
|---|---|---|
| Flexibility | Easy to adjust permissions | Risk of excessive permissions |
| Control | Owners have direct oversight | Potential for security weaknesses |
| Implementation | Straightforward to set up | Limited centralized auditing |
| Cost | Lower initial expenses | Higher maintenance over time |
| Scalability | Works well for smaller setups | Challenging for larger systems |
DAC works best in environments where quick, user-driven access decisions are essential, and resource owners have a clear understanding of security requirements. However, organizations must carefully manage permissions to avoid security risks.
Mandatory Access Control (MAC)
Mandatory Access Control (MAC) enforces a centralized security policy, assigning access rights based on user clearance levels and data classification.
How MAC Works
MAC uses a hierarchical security model, assigning both users and resources specific levels of classification. Common classifications include:
- Top Secret: The highest security clearance
- Secret: A step below Top Secret
- Confidential: A moderate clearance level
- Unclassified: The lowest level
The system relies on the Bell-LaPadula model, which enforces two core rules:
- No Read Up: Users can't access data above their clearance level.
- No Write Down: Users can't write data to a level below their clearance.
Where MAC Is Used
MAC is ideal for environments that demand strict access control, such as:
- Government Facilities: Handling classified documents.
- Military Installations: Securing command centers and restricted zones.
- Research Labs: Protecting sensitive experiments and materials.
- Financial Institutions: Controlling access to vaults and secure trading floors.
System administrators manage access policies centrally, ensuring consistent enforcement across all areas.
MAC: Strengths and Challenges
| Aspect | Characteristics | Impact |
|---|---|---|
| Security Level | Extremely high | Prevents unauthorized access effectively. |
| Implementation | Complex | Requires a detailed classification system. |
| Maintenance | Centralized | Simplifies long-term management. |
| Flexibility | Limited | Changes demand system-wide updates. |
| Compliance | Strong | Aligns with strict regulatory standards. |
MAC's rigid structure ensures tight security and clear audit trails, making it a strong choice for organizations prioritizing data protection. However, its lack of flexibility can slow operations, so organizations must balance security needs with practical workflow requirements.
Attribute-Based Access Control (ABAC)
Attribute-Based Access Control (ABAC) provides flexible, real-time access decisions by analyzing a combination of attributes. It takes into account user details, environmental factors, and resource-specific properties to determine who can access what.
Key Elements of ABAC
ABAC works by evaluating four main categories of attributes:
- Subject Attributes: Details about the user, such as their role, department, or clearance level.
- Resource Attributes: Information about the resource, like its classification, sensitivity, or location.
- Action Attributes: The type of action being requested, such as reading, writing, deleting, or modifying.
- Environmental Attributes: External factors, including time, physical location, or security conditions.
These attributes are processed through predefined rules. For instance, a rule might specify: "If the user belongs to the maintenance department, it’s between 8:00 AM and 5:00 PM, and they are in Building A, grant access to mechanical room controls."
This rule-based approach makes ABAC highly adaptable to different scenarios.
How ABAC Works in Practice
ABAC’s dynamic framework allows for tailored access control across various situations. Here’s an example of how it might be applied:
| Access Scenario | Required Attributes | Authorization Logic |
|---|---|---|
| Server Room Entry | Department: IT Time: 24/7 Clearance: Level 2+ |
All attributes must match |
| HVAC Controls | Role: Maintenance Time: Business hours Location: On-premise |
Any two attributes sufficient |
| Security Feeds | Department: Security Shift: Active Emergency status: Any |
Priority override available |
Why ABAC Stands Out
ABAC offers several advantages for managing access in facilities:
1. Improved Security
It provides fine-tuned control by dynamically adjusting permissions. For example, access can be restricted during off-hours or heightened during emergencies.
2. Streamlined Operations
ABAC automates access decisions using preset rules, reducing the need for manual updates and saving time.
3. Compliance Support
The system tracks attributes and access events, creating detailed logs that help meet regulatory and security requirements.
4. Easily Scalable
As facilities expand or change, ABAC can scale effortlessly. Adding new areas or resources is as simple as defining their attributes, with the existing rules handling the rest.
Rule-Based Access Control
Rule-Based Access Control relies on administrator-defined rules to manage who can access specific areas of a facility. These rules must be clear, precise, and adaptable to meet changing security requirements.
Setting Up the Rule System
You can configure Rule-Based Access Control through a centralized interface, following these steps:
- Define Rules: Set clear access conditions, including specific actions, priority levels, and time-based restrictions. This allows you to manage access during certain hours or for particular situations.
- Assign Access Zones: Divide the facility into zones and apply rule sets based on their security requirements. For example, high-security areas may need stricter rules, while public zones can have more relaxed access. Ensure emergency exits and critical areas comply with safety regulations.
- Test and Refine Rules: Simulate the rules in a controlled setting to verify they work as intended. Check for conflicts between rules and ensure emergency protocols override standard ones when necessary. Be ready to update rules quickly for temporary adjustments.
Conclusion
Modern access control systems address facility security requirements through various approaches, each with its own strengths:
- RBAC (Role-Based Access Control): Relies on defined roles to manage permissions, making it suitable for diverse security requirements.
- DAC (Discretionary Access Control): Grants resource owners control, allowing quick and flexible access changes.
- MAC (Mandatory Access Control): Provides centralized, strict control, ideal for highly sensitive environments.
- ABAC (Attribute-Based Access Control): Utilizes real-time factors like time, location, and user details for dynamic security.
- Rule-Based Access Control: Simplifies management with clear, administrator-defined rules.
Choosing the right system requires assessing your facility's specific security needs and compliance requirements to strike a balance between strong protection and smooth operations.
